Europe is known for its incredible diversity and immense cultural wealth, and this holds as well when it comes to education. With various impressive universities spread across the continent, plenty of higher learning opportunities are […]
- January 27th, 2023
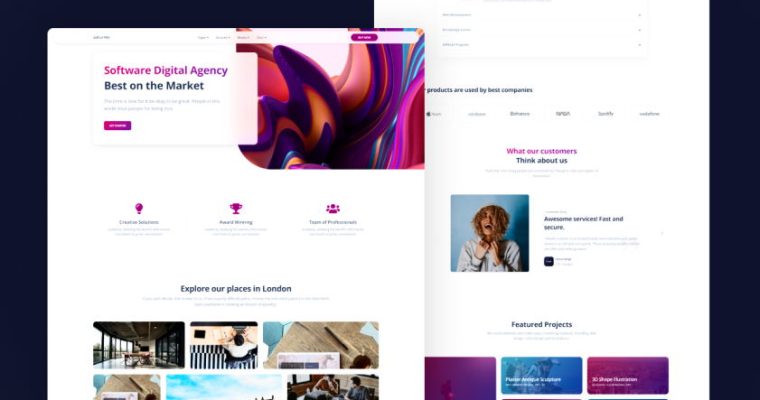
Innovation is a powerful tool. It can propel businesses and organizations to new heights of success, providing them with competitive advantages that set them apart from their competitors. In terms of the European Information Technology […]
- December 30th, 2022
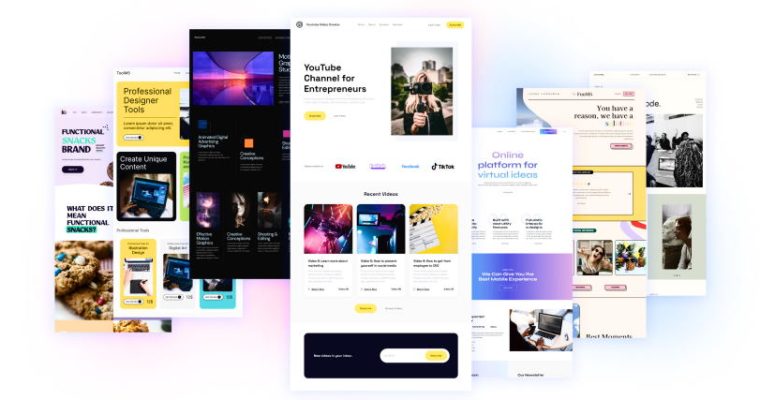
As the world’s leading regions in technology and design, the United States and Europe take very different approaches to website design. Home to Silicon Valley, the US is known for its cutting-edge language combinations and […]
- December 6th, 2022
The European Union is facing a major energy crisis. This has raised questions about the ability of countries to access reliable and secure sources of electricity, which in turn poses many implications for IT infrastructure […]
- November 8th, 2022
If you are a web design business looking to expand into new markets and take your services global, then the European market could be the perfect opportunity. With an estimated population of over 750 million […]
As the Internet of Things (IoT) continues to revolutionize global industries, we’re seeing a dramatic shift in how countries around the world are approaching IoT policy. In Europe, these changes have become particularly noticeable due […]
- September 12th, 2022
The digitalization of organizations, businesses, and services has created a new technological industry in Europe – web development. With the growing need for custom websites that can meet the demands of future technology landscapes, experienced […]
- August 15th, 2022
European Union leadership has long been a driving force in promoting innovation and international cooperation. In recent years, the EU has begun to focus on blockchain technologies, recognizing these decentralized networks’ potential for revolutionizing the […]
- July 19th, 2022
Are you an EU-based web design professional who needs to protect your project property from potential copyright infringement? This can be tricky, especially when dealing with international projects and clients. Thankfully, understanding the copyright laws […]
- June 16th, 2022
The European AI market is rapidly growing and represents a significant opportunity for major players in the technology industry. With investments in AI-related technology continuously increasing throughout Europe, it is important to understand the key […]
Tips For Streamlining Payment Processing For Web Development Projects

Are you a web development agency faced with the challenge of increasing cash flow so that you can scale your business? Processing payments for web development projects is an area of your operations that must be streamlined to send money to Poland from Norway – and to keep clients satisfied. The good news is there are ways to increase efficiency and maximize project revenue without sacrificing customer satisfaction during payment processing. In this blog post, we’ll look at several tips that will help you speed up payment processing for your web development projects. Read on to learn more!
alphabet Recent Post
-

Guide to Master’s Degrees in Web Design Across Europe
Comments Off on Guide to Master’s Degrees in Web Design Across Europe Jan 8, 2023 -

Revolutionary Potential of Innovation in European Information Technology
Comments Off on Revolutionary Potential of Innovation in European Information Technology Jan 8, 2023 -

USA and Europe Divide: Exploring the Different Approaches to Website Design
Comments Off on USA and Europe Divide: Exploring the Different Approaches to Website Design Jan 8, 2023
We are a Web Design & IT Company located in Europe that helps companies grow!
![The [204] Design Collective](https://www.the204designcollective.com/wp-content/uploads/PIC-LOGO_2.png)